From bgr.com
A new vulnerability was found on M1 Mac and newer models that allow hackers to extract encryption keys. This issue is unpatchable, which means every Mac user could be compromised, but it doesn’t mean you should freak out.
As first reported by Ars Technica, an academic research paper highlights this unpatchable vulnerability that can extract encryption keys from M1 Mac and newer models.
The researcher named this vulnerability GoFetch, a “microarchitectural side-channel attack that can extract secret keys from constant-time cryptographic implementations via data memory-dependent prefetchers (DMPs).”
They have found this issue with M1 Mac devices but found that M2 and M3 CPUs also exhibit “similar exploitable DMP behavior.” They have not tested with other chip variants, such as M1 Max, M2 Pro, etc., but the researchers hypothesize that they’re likely to be exploited as well.
How can you protect your M1 Mac against this attack?
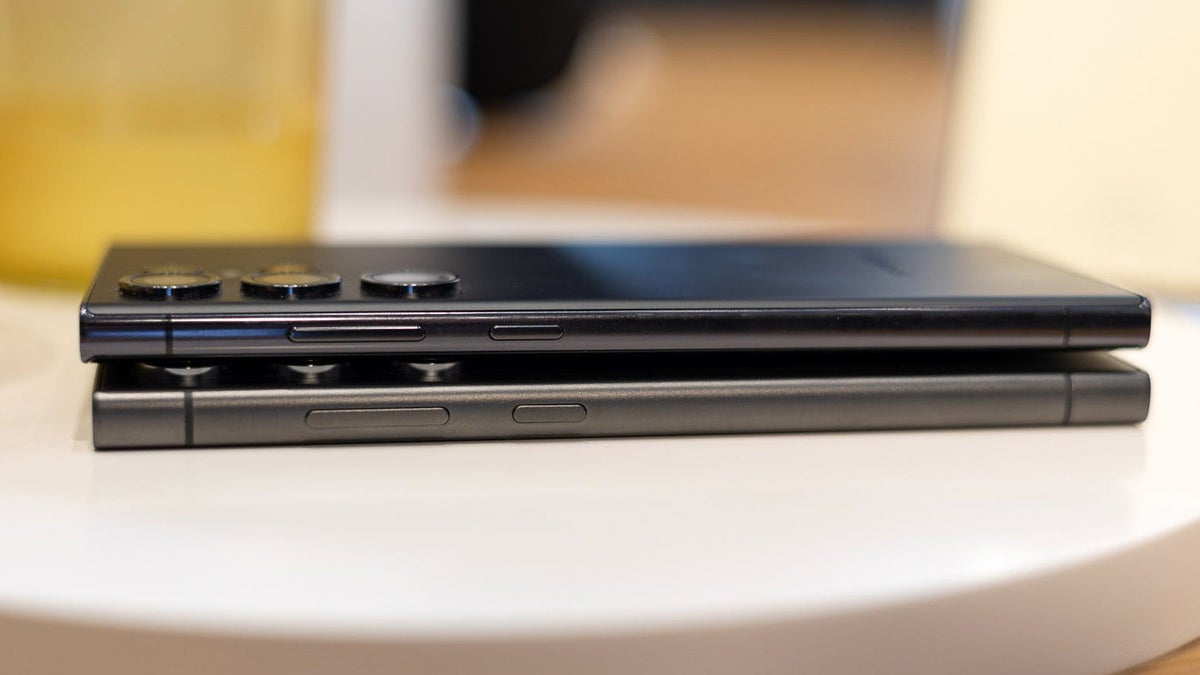
 Image source: Christian de Looper for BGR
Image source: Christian de Looper for BGRThe researchers say that the best way to protect yourself is by constantly updating your Mac to the latest version of macOS. For developers of cryptographic libraries, they can either set the DOIT bit and DIT bit bits, which disable the DMP on some CPUs, such as M3 processors.
[ For more curated tech news, check out the main news page here]
The post M1 Mac and newer models have an unpatchable vulnerability first appeared on bgr.com


/cdn.vox-cdn.com/uploads/chorus_asset/file/25546607/image__21_.png)