A new Rust-based macOS malware spreading as a Visual Studio update to provide backdoor access to compromised systems uses infrastructure linked to the infamous ALPHV/BlackCat ransomware gang.
The campaign delivering the backdoor started since at least November 2023 and is still underway distributing newer variants of the malware.
Written in Rust, the malware can run on Intel-based (x86_64) and ARM (Apple Silicon) architectures, say researchers at cybersecurity company Bitdefender, who are tracking it as RustDoor.
Potential link to ransomware operations
While analyzing RustDoor, malware researchers at Bitdefender discovered that the malware communicated with four command and control (C2) servers.
Looking at threat intelligence data, the analysts found that three of them had been used in attacks potentially linked to ransomware attacks from an ALPHV/BlackCat affiliate.
However, the researchers highlight that this is insufficient evidence to confidently link the use of RustDoor to a particular threat actor and that “artifacts and IoCs [indicators of compromise] suggest a possible relationship with the BlackBasta and ALPHV/BlackCat ransomware operators.”
With cybercriminals having less freedom in choosing their infrastructure and being restricted to hosting services that provide anonymity and condone illegal activity, it is common for multiple threat actors to use the same servers for attacks.
While encryptors for the macOS system exist, builds for Apple M1 from LockBit created before December 2022, there are no public reports at this time of ransomware attacking Apple’s operating system.
Most operations target Windows and Linux systems as enterprise environments use servers running these operating systems.
Distribution details
RustDoor is distributed primarily as an updater for Visual Studio for Mac, Microsoft’s integrated development environment (IDE) for the macOS platform, which will be discontinued this year on August 31.
The macOS backdoor is delivered under multiple names, including ‘zshrc2,’ ‘Previewers,’ ‘VisualStudioUpdater,’ ‘VisualStudioUpdater_Patch,’ ‘VisualStudioUpdating,’ ‘visualstudioupdate,’ and ‘DO_NOT_RUN_ChromeUpdates‘.
According to Bitdefender, the malware has been under active distribution and have been undetected for at least three months.
The researchers discovered three versions of the malware, which come as FAT binaries that include Mach-O files for both x86_64 Intel and ARM architectures but do not come bundled in typical parent files such as Application Bundles or Disk Image.
Bitdefender says this atypical distribution method reduces the campaign’s digital footprint and the likelihood of security products flagging the backdoor as suspicious.
Backdoor capabilities
In a report this week, the researchers say that RustDoor has commands to control the compromised system and to exfiltrate data, and it can persist on the device by modifying system files.
After infecting a system, the malware communicates with command and control (C2) servers using specific endpoints for registration, task execution, and data exfiltration.
The commands supported by the malware include the following:
- ps: Lists running processes, useful for monitoring system activity.
- shell: Executes arbitrary shell commands, giving attackers direct control.
- cd: Changes the current directory, allowing navigation through the file system.
- mkdir: Creates a new directory, useful for organizing stolen data or malware components.
- rm: Removes files, potentially for deleting important files or cleaning up traces of the malware.
- rmdir: Removes directories, similar to rm but for directories.
- sleep: Pauses execution for a set time, possibly to evade detection or synchronize actions.
- upload: Sends files to a remote server, used for exfiltrating stolen data.
- botkill: Terminates other malware processes, possibly to eliminate competition or free system resources.
- dialog: Displays messages or prompts to the user, potentially for phishing or to execute commands with user privileges.
- taskkill: Ends specified processes, useful for stopping security software or other processes interfering with malware.
- download: Retrieves files from a remote server, used for bringing additional malware components or updates onto the infected system.
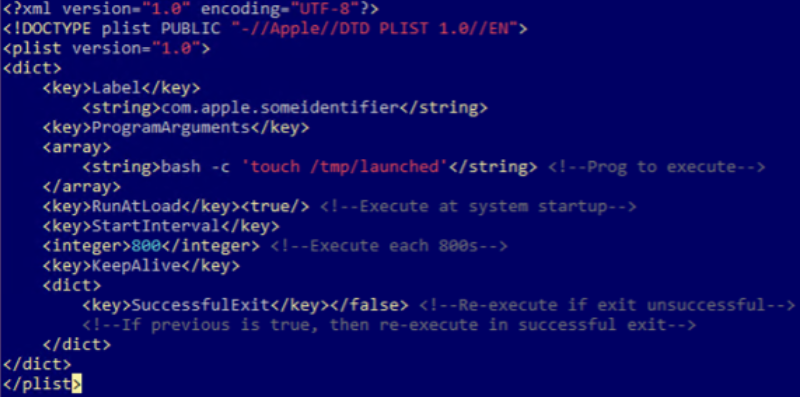
The backdoor uses Cron jobs and LaunchAgents to schedule its execution at specific times or when the user logs in, thus making sure it survives system reboots.
Moreover, it modifies the ~/.zshrc file to execute in new terminal sessions or add it to the Dock with system commands, which helps it blend in with legitimate applications and user activities.
Bitdefender notes that there are at least three variants of RustDoor, the earliest one seen since early October 2023.
The next one was seen November 22 and appeared to be a testing version that preceded an updated version observed on November 30, which includes “a complex JSON configuration as well as an embedded Apple script used for exfiltration” of files with specific extensions.
The researchers provide a list of known indicators of compromise for RustDoor, which includes binaries, download domains, and URLs for the four command and control servers discovered.
[ For more curated Apple news, check out the main news page here]
The post New RustDoor macOS malware impersonates Visual Studio update first appeared on www.bleepingcomputer.com


/cdn.vox-cdn.com/uploads/chorus_asset/file/25546607/image__21_.png)